
February 2026: Six Actively Exploited Zero‑Days — An Unprecedented Warning for the Industry
Microsoft February 2026 Patch Tuesday just landed, and it’s already being called one of the most urgent security releases in years.
Six actively exploited zero‑days.
Not hypothetical.
Not “under limited attack.”These vulnerabilities are being weaponized in the wild right now — and the financial sector is squarely in the blast radius.
For Financial Advisors, IMOs, and BGA owners, this month’s release isn’t just another routine patch cycle. It’s a direct reminder that:
• Your endpoints are being targeted
• Your vendors are being targeted
• Your advisors’ home networks are being targeted
• And your compliance obligations under NYDFS, SEC, and state regulators don’t pause just because attackers move faster than your patching schedule
This month’s vulnerabilities hit core components that many firms rely on daily — including Windows, Office, identity layers, and authentication mechanisms. When attackers are already exploiting these flaws, delayed patching becomes a business risk, not an IT inconvenience.
🛡️ What This Means for Regulated Financial Organizations
If you operate in a regulated environment, this Patch Tuesday should trigger immediate internal questions:
1️⃣ Are all endpoints — including remote and advisor‑owned devices — covered by centralized patching?
If not, you’re exposed.
Advisors working from home, shared devices, and unmanaged laptops are now the easiest entry points for attackers.
2️⃣ Do you have evidence‑based patch management for DFS audits?
“IT says it’s patched” is not documentation.
DFS expects proof, not assumptions — and auditors increasingly ask for patch logs, timelines, and remediation workflows.
3️⃣ Are you monitoring for exploitation attempts tied to these CVEs?
Threat actors don’t wait for your maintenance window.
They move within hours, not weeks.
This is the kind of month where firms with weak patch governance get breached — and firms with strong governance get validated
🔐 How JND Consulting Group Helps You Stay Ahead
JND Consulting Group supports IMOs, BGAs, and advisory firms with cybersecurity programs built for regulated financial environments. Our services include:
- ✔️ Patch & vulnerability management programs
- ✔️ Zero‑Trust hardening for hybrid and remote workforces
- ✔️ Continuous monitoring & threat detection
- ✔️ DFS‑aligned cybersecurity governance & documentation
- ✔️ Incident response planning and readiness
When attackers are exploiting six zero‑days at once, “we’ll get to it next week” is no longer an option.
Your clients expect protection. Regulators demand proof. Your business deserves both.
📣 The Threat Landscape Just Escalated
If you want help assessing your exposure or tightening your patching program, JND Consulting Group is here to support you.
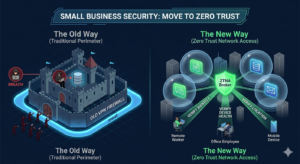
Why “Never Trust, Always Verify” is the New Standard: A Small Business Guide to ZTNA
Facebook X LinkedIn Why ZTNA is the New Standard for Small Business In the traditional world of office work, cybersecurity was like a castle moat.

Why RIAs Are Now Prime Targets for Cyberattacks in 2025–2026
Facebook Twitter LinkedIn Registered Investment Advisors (RIAs) have quietly become one of the most attractive targets for cybercriminals—and the threat is accelerating. While large financial

Is Your Cloud Data Truly Safe? Why Microsoft 365 and Google Workspace Need Third-Party Backup
Facebook Twitter LinkedIn Is Your Cloud Data Truly Safe? Why Microsoft 365 and Google Workspace Need Third-Party Backup In today’s cloud-first world, most businesses rely
