Why ZTNA is the New Standard for Small Business
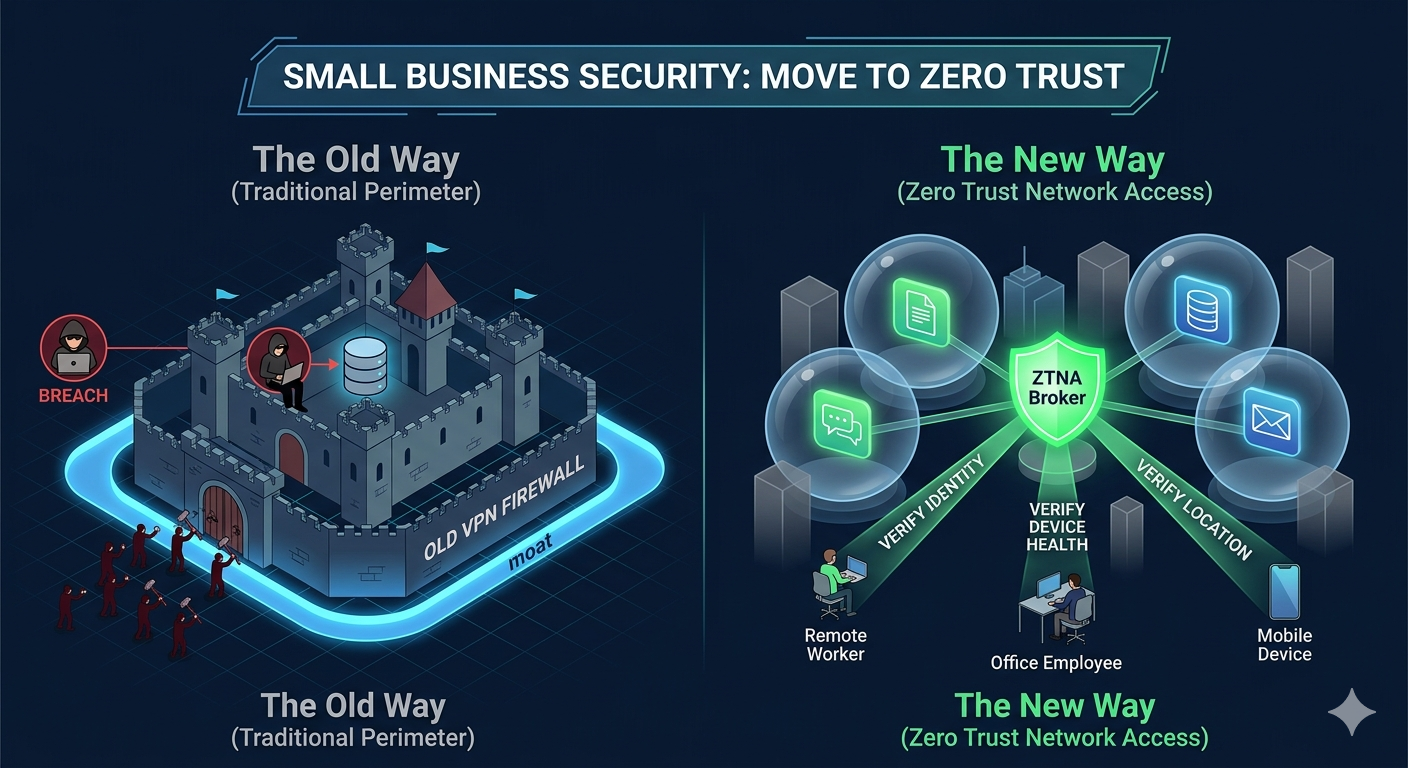
In the traditional world of office work, cybersecurity was like a castle moat. As long as you were inside the office walls, you were “trusted” and had access to everything. But in 2026, the walls have crumbled. With remote teams, cloud apps like Microsoft 365, and mobile devices, the “moat” strategy no longer works.
Enter Zero Trust Network Access (ZTNA).
What is Zero Trust Network Access (ZTNA)?
According to Microsoft Security, ZTNA is a security model built on one simple rule: Never trust, always verify. Instead of granting a user access to the entire network once they log in, ZTNA treats every single request as a potential threat. It doesn’t matter if you are sitting in the headquarters or a coffee shop; the system verifies your identity, your device health, and your location before letting you touch a specific application.
The Three Pillars of ZTNA:
Verify Explicitly: Always authenticate based on all available data points (identity, location, device health, service, or workload).
Use Least Privilege Access: Users only get access to the specific apps they need for their job—nothing more.
Assume Breach: Operates under the mindset that the network has already been compromised, using end-to-end encryption and constant monitoring to minimize damage.
Why Small Businesses Must Move to ZTNA Now
For a long time, small business owners thought they were “too small to be targeted.” In 2026, that is a dangerous myth. Small businesses are often the preferred targets because their security is easier to crack.
1. The Death of the VPN
Traditional VPNs are clunky, slow, and—worst of all—dangerous. Once a hacker steals a VPN password, they have the “keys to the castle” and can move laterally through your entire network. ZTNA replaces the VPN by connecting users directly to the application, not the network.
2. Supporting the “Work from Anywhere” Reality
Whether your team is using a personal laptop (BYOD) or a company-issued tablet, ZTNA ensures that only “healthy” devices can connect. If an employee’s laptop is missing a security update, ZTNA can block access until it’s patched, preventing a virus from jumping into your cloud files.
3. Lowering Insurance Premiums
Cyber insurance providers are increasingly requiring Zero Trust protocols. By implementing ZTNA, small businesses can demonstrate “proactive risk management,” which often leads to better coverage and lower premiums.
How JND Consulting Group Can Help
Navigating the transition from old-school firewalls to a modern Zero Trust environment can be overwhelming. JND Consulting Group specializes in taking enterprise-grade security and making it accessible for small-to-mid-sized businesses.
Our ZTNA Implementation Strategy:
Comprehensive Inventory: We conduct a thorough audit of your system to uncover gaps and “ghost” applications that are putting your network at risk.
Identity-First Security: We help you deploy Multi-Factor Authentication (MFA) and Conditional Access policies, ensuring that only the right people get in.
24/7 Monitoring via our SOC: Implementation is only half the battle. JND provides a Managed Security Operations Center (SOC) to monitor your network in real-time, catching anomalies before they become breaches.
Compliance Alignment: Whether you deal with HIPAA, PCI, or SOX, we ensure your ZTNA setup meets strict regulatory requirements, providing you with a “compliance portal” to make audits painless.
Stop Gambling with Your Data
In today’s threat landscape, “good enough” security is an invitation for disaster. Let JND Consulting Group build a “winning gameplan” for your business.
Ready to modernize your security?
Connect with a Team Expert for a security health check.
Why “Never Trust, Always Verify” is the New Standard: A Small Business Guide to ZTNA
Facebook X LinkedIn Why ZTNA is the New Standard for Small Business In the traditional world of office work, cybersecurity was like a castle moat.

Why RIAs Are Now Prime Targets for Cyberattacks in 2025–2026
Facebook Twitter LinkedIn Registered Investment Advisors (RIAs) have quietly become one of the most attractive targets for cybercriminals—and the threat is accelerating. While large financial

Is Your Cloud Data Truly Safe? Why Microsoft 365 and Google Workspace Need Third-Party Backup
Facebook Twitter LinkedIn Is Your Cloud Data Truly Safe? Why Microsoft 365 and Google Workspace Need Third-Party Backup In today’s cloud-first world, most businesses rely
